Explanation/Reference:
Data Terminal Equipment (DTE) - Usually a customer owned device that provides connectivity between company's own network and the frame relay's network.
For your exam you should know below information about WAN Technologies:
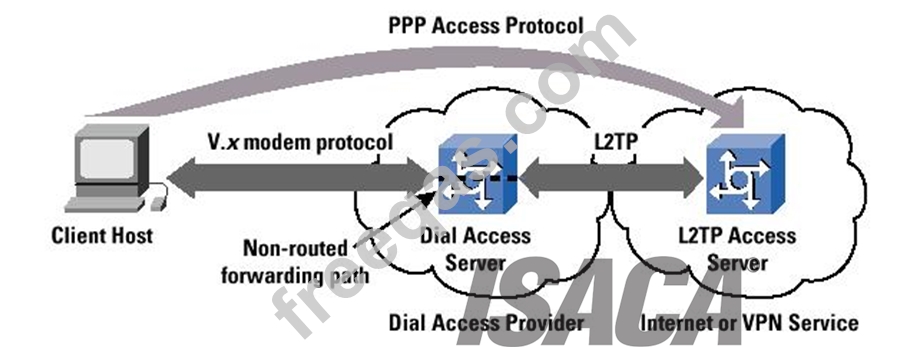
Point-to-point protocol
PPP (Point-to-Point Protocol) is a protocol for communication between two computers using a serial interface, typically a personal computer connected by phone line to a server. For example, your Internet server provider may provide you with a PPP connection so that the provider's server can respond to your requests, pass them on to the Internet, and forward your requested Internet responses back to you.
PPP uses the Internet protocol (IP) (and is designed to handle other protocol as well). It is sometimes considered a member of the TCP/IP suite of protocols. Relative to the Open Systems Interconnection (OSI) reference model, PPP provides layer 2 (data-link layer) service. Essentially, it packages your computer's TCP/IP packets and forwards them to the server where they can actually be put on the Internet.
PPP is a full-duplex protocol that can be used on various physical media, including twisted pair or fiber optic lines or satellite transmission. It uses a variation of High Speed Data Link Control (HDLC) for packet encapsulation.
PPP is usually preferred over the earlier de facto standard Serial Line Internet Protocol (SLIP) because it can handle synchronous as well as asynchronous communication. PPP can share a line with other users and it has error detection that SLIP lacks. Where a choice is possible, PPP is preferred.
Point-to-point protocol
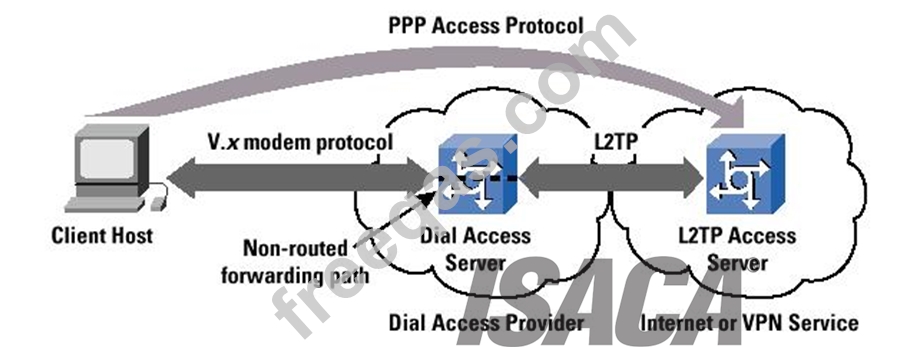
Image from:http://withfriendship.com/images/g/31728/a-pointtopoint-protocol.png
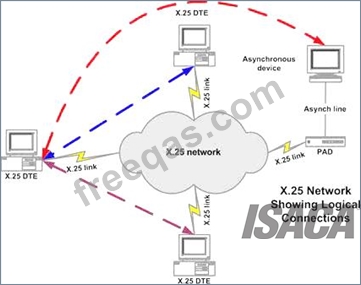
X.25
X.25 is an ITU-T standard protocol suite for packet switched wide area network (WAN) communication.
X.25 is a packet switching technology which uses carrier switch to provide connectivity for many different networks.
Subscribers are charged based on amount of bandwidth they use. Data are divided into 128 bytes and encapsulated in High Level Data Link Control (HDLC).
X.25 works at network and data link layer of an OSI model.
X.25
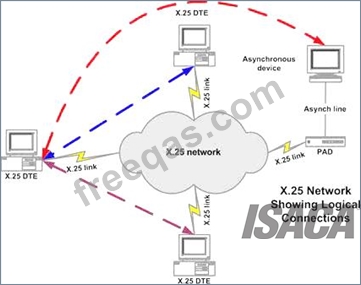
Image from:http://www.sangoma.com/assets/images/content/tutorials_x25_1.gif Frame Relay Works as packet switching Operates at data link layer of an OSI model Companies that pay more to ensure that a higher level of bandwidth will always be available, pay a committed information rate or CIR Two main types of equipment's are used in Frame Relay
1. Data Terminal Equipment (DTE) - Usually a customer owned device that provides connectivity between company's own network and the frame relay's network.
2. Data Circuit Terminal Equipment (DCE) - Service provider device that does the actual data transmission and switching in the frame relay cloud.
The Frame relay cloud is the collection of DCE that provides that provides switching and data communication functionality. Frame relay is any to any service.
Frame Relay
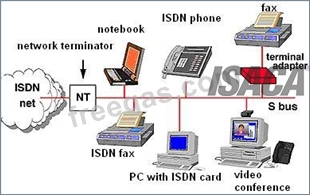
Image from: http://www.cpcstech.com/images/frame-2.jpg
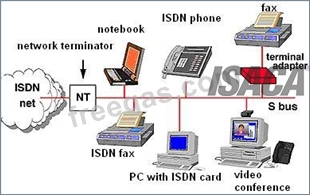
Integrated Service Digital Network (ISDN)
Enables data, voice and other types of traffic to travel over a medium in a digital manner previously used only for analog voice transmission.
Runs on top of the Plain Old Telephone System (POTS). The same copper telephone wire is used.
Provide digital point-to-point circuit switching medium.
ISDN
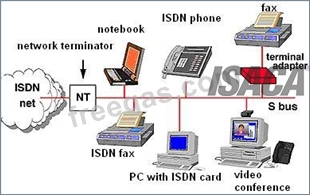
Image from: http://www.hw-server.com/obrazek/network_topology
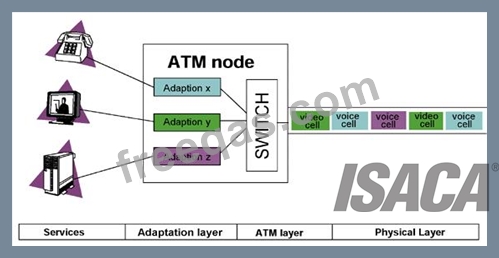
Asynchronous Transfer Mode (ATM)
Uses Cell switching method
High speed network technology used for LAN, MAN and WAN
Like frame relay it is connection oriented technology which creates and uses fixed channel Data are segmented into fixed size cell of 53 bytes Some companies have replaces FDDI back-end with ATM Asynchronous Transfer Mode
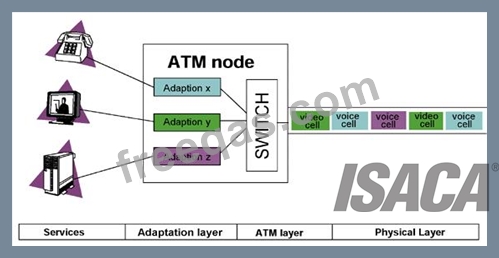
Image from: http://html.rincondelvago.com/000050700.png
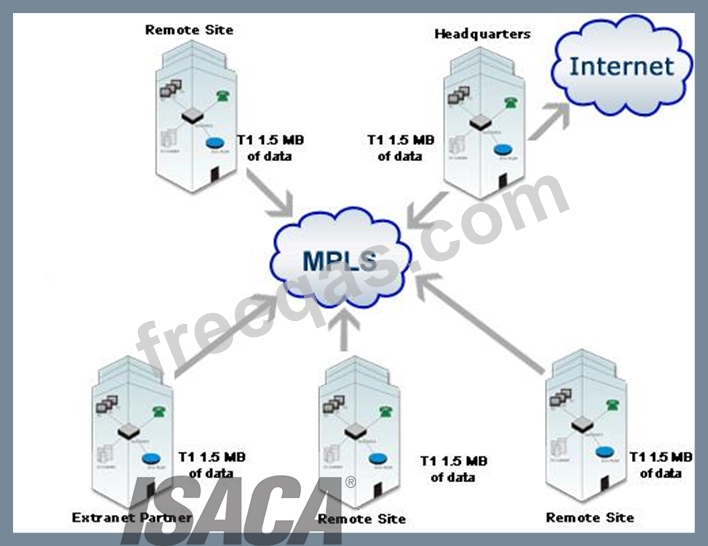
Multiprotocol Label Switching (MPLS)
Multiprotocol Label Switching (MPLS) is a standard-approved technology for speeding up network traffic flow and making things easier to manage.MPLS involves setting up a specific path for a given sequence of packets, identified by a label put in each packet, thus saving the time needed for a router to look up the address to the next node to forward the packet to.
MPLS is called multiprotocol because it works with the Internet Protocol (IP), Asynchronous Transport Mode (ATM), and frame relay network protocols.
In reference to the Open Systems Interconnection, or OSI model, MPLS allows most packets to be forwarded at Layer 2 (switching) level rather than at the Layer 3 (routing) level.
In addition to moving traffic faster overall, MPLS makes it easy to manage a network for quality of service (QoS). For these reasons, the technique is expected to be readily adopted as networks begin to carry more and different mixtures of traffic.
MPLS
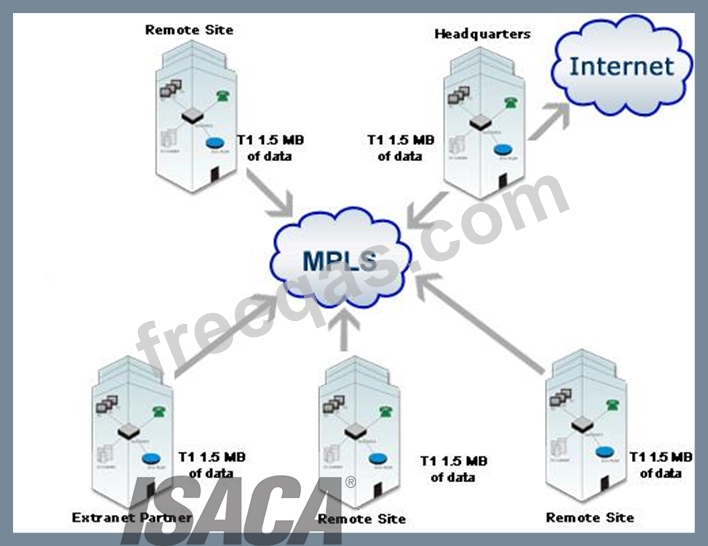
Image from: http://www.carrierbid.com/wp-content/uploads/2011/01/mpls1.gif The following answers are incorrect:
DCE - Data Circuit Terminal Equipment (DCE) is a service provider device that does the actual data transmission and switching in the frame relay cloud.
DME - Not a valid frame relay technique
DLE - Not a valid frame relay technique
The following reference(s) were/was used to create this question:
CISA review manual 2014 page number 266