A black hat hacker is enumerating a network and wants to remain covert during the process. The hacker initiates a vulnerability scan. Given the task at hand the requirement of being covert, which of the following statements BEST indicates that the vulnerability scan meets these requirements?
After correctly configuring a new wireless enabled thermostat to control the temperature of the company's meeting room, Joe, a network administrator determines that the thermostat is not connecting to the internet-based control system. Joe verifies that the thermostat received the expected network parameters and it is associated with the AP. Additionally, the other wireless mobile devices connected to the same wireless network are functioning properly. The network administrator verified that the thermostat works when tested at his residence.
Which of the following is the MOST likely reason the thermostat is not connecting to the internet?
Which of the following are examples of two-factor authentication? (Select THREE)
Joe a website administrator believes he owns the intellectual property for a company invention and has
been replacing image files on the company's public facing website in the DMZ. Joe is using steganography
to hide stolen data.
Which of the following controls can be implemented to mitigate this type of inside threat?
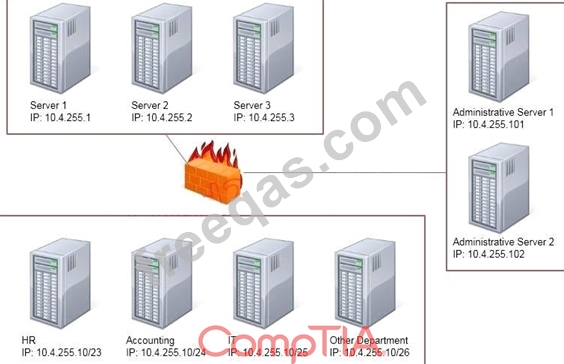
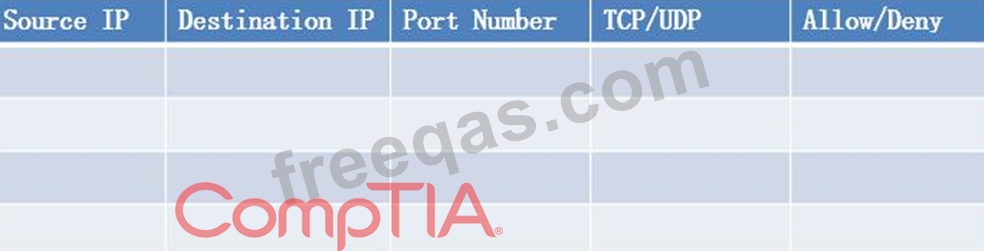
Task: Configure the firewall (fill out the table) to allow these four rules:
Only allow the Accounting computer to have HTTPS access to the Administrative server.
Only allow the HR computer to be able to communicate with the Server 2 System over SCP.
Allow the IT computer to have access to both the Administrative Server 1 and Administrative Server 2